The control panel of a Ski lift in Austria was exposed online, the disconcerting discovery was made on March 16 by the security experts Tim Philipp Schäfers and Sebastian Neef with security organization InternetWache.org.
The ski lift is Patscherkofelbahn, a sky facility that connects the village of Igls with the Patscherkofel resort.
The two researchers promptly reported the discovery to the Austrian Computer Emergency and Response Team (CERT).
“We have also done in this case: we received the message on a Friday afternoon, we passed it on later in the evening to our contact in Innsbruck.” reported the CERT in a blog post.
Officials from the city of Innsbruck have shut down the ski lift after the security duo has reported their findings.
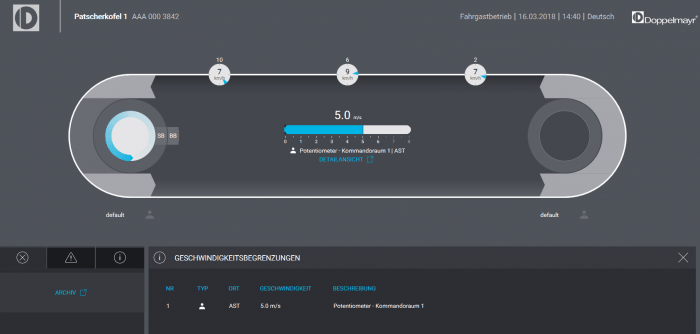
“The control of the Patscherkofelbahn was accessible via a web interface unencrypted and without the need for authentication via the Internet. In addition, the corresponding control software was not up to date, but pointed to one of us found and reported to the manufacturer vulnerability, “says Schäfers.
The experts discovered the Human Machine Interface used to control the ski lift was exposed online without authentication.
An attacker with access to the Human Machine Interface is in the position to control several settings for the sky facility, including the speed, the distance between cable cars, and the cable tension.
The two researchers promptly reported the discovery to the Austrian Computer Emergency and Response Team (CERT) that passed their contact to the authorities at the city of Innsbruck.
As a precautionary measure, the authorities shut down the Patscherkofelbahn ski lift and started a security audit, at the time of writing the facility is still offline.
While the experts were reporting their discovery to Innsbruck officials, the NBC media outlet shared a footage of a malfunctioning ski lift in the ski resort of Gudauri, Georgia.
Even if the Gudauri accident is not linked to any other event occurred at Patscherkofelbahn. media noticed that the ski lifts in both facilities are manufactured by the Austrian firm Doppelmayr.
The CERT Austria confirmed that the problem has been solved and Innsbruck officials are plans to deploy a secure system before the summer season opens.